
Want to know Exambible 250-438 Exam practice test features? Want to lear more about Symantec Administration of Symantec Data Loss Prevention 15 certification experience? Study 100% Guarantee Symantec 250-438 answers to Latest 250-438 questions at Exambible. Gat a success with an absolute guarantee to pass Symantec 250-438 (Administration of Symantec Data Loss Prevention 15) test on your first attempt.
Free 250-438 Demo Online For Symantec Certifitcation:
NEW QUESTION 1
Refer to the exhibit. Which type of Endpoint response rule is shown?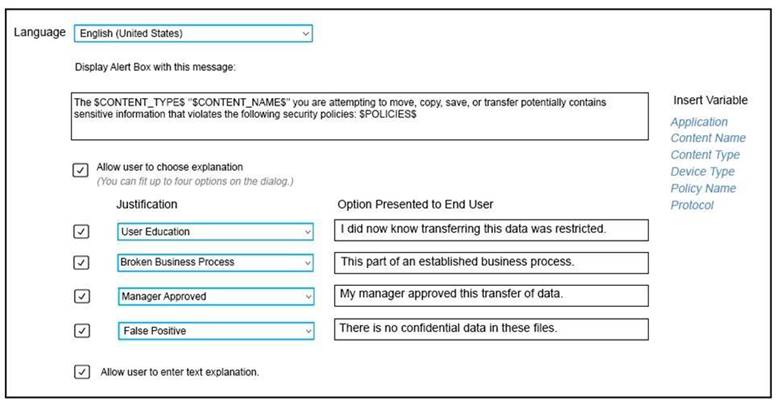
Answer: B
Explanation:
Reference: https://help.symantec.com/cs/dlp15.0/DLP/v27595430_v120691346/Configuring-the-Endpoint-Prevent:-Block-action?locale=EN_US
NEW QUESTION 2
Which two technologies should an organization utilize for integration with the Network Prevent products? (choose two.)
Answer: CD
Explanation:
Reference: https://www.symantec.com/connect/articles/network-prevent
NEW QUESTION 3
Which option correctly describes the two-tier installation type for Symantec DLP?
Answer: D
Explanation:
Reference: https://www.symantec.com/connect/forums/deployment-enforce-and-detection-servers
NEW QUESTION 4
A DLP administrator has performed a test deployment of the DLP 15.0 Endpoint agent and now wants to uninstall the agent. However, the administrator no longer remembers the uninstall password. What should the administrator do to work around the password problem?
Answer: D
NEW QUESTION 5
A DLP administrator is attempting to add a new Network Discover detection server from the Enforce management console. However, the only available options are Network Monitor and Endpoint servers. What should the administrator do to make the Network Discover option available?
Answer: C
NEW QUESTION 6
Which option is an accurate use case for Information Centric Encryption (ICE)?
Answer: B
Explanation:
Reference: https://help.symantec.com/cs/ICE1.0/ICE/v126756321_v120576779/Using-ICE-with-Symantec-Data-Loss-Preventionabout_dlp?locale=EN_US
NEW QUESTION 7
An organization wants to restrict employees to copy files only a specific set of USB thumb drives owned by the organization.
Which detection method should the organization use to meet this requirement?
Answer: D
NEW QUESTION 8
What detection server is used for Network Discover, Network Protect, and Cloud Storage?
Answer: B
Explanation:
Reference: https://help.symantec.com/cs/dlp15.0/DLP/v16110606_v120691346/Modifying-the-Network-Discover-Cloud-Storage-Discover-Server-configuration?locale=EN_US
NEW QUESTION 9
A company needs to implement Data Owner Exception so that incidents are avoided when employees send or receive their own personal information.
What detection method should the company use?
Answer: C
Explanation:
Reference: https://help.symantec.com/cs/dlp15.5/DLP/v40148006_v128674454/About-Data-Owner-Exception?locale=EN_US
NEW QUESTION 10
What detection technology supports partial contents matching?
Answer: A
Explanation:
Reference: https://help.symantec.com/cs/dlp15.1/DLP/v115965297_v125428396/Mac-agent-detection-technologies?locale=EN_US
NEW QUESTION 11
Which service encrypts the message when using a Modify SMTP Message response rule?
Answer: D
Explanation:
Reference: https://www.symantec.com/connect/articles/network-prevent
NEW QUESTION 12
Which statement accurately describes where Optical Character Recognition (OCR) components must be installed?
Answer: C
Explanation:
Reference: https://help.symantec.com/cs/dlp15.0/DLP/v122760174_v120691346/Setting-up-OCR-Servers?locale=EN_US
NEW QUESTION 13
An administrator is unable to log in to the Enforce management console as “sysadmin”. Symantec DLP is configured to use Active Directory authentication. The administrator is a member of two roles: “sysadmin” and “remediator.” How should the administrator log in to the Enforce console with the “sysadmin” role?
Answer: C
NEW QUESTION 14
Where should an administrator set the debug levels for an Endpoint Agent?
Answer: C
Explanation:
Reference: https://support.symantec.com/en_US/article.TECH248581.html
NEW QUESTION 15
What is the Symantec recommended order for stopping Symantec DLP services on a Windows Enforce server?
Answer: D
Explanation:
Reference: https://help.symantec.com/cs/dlp15.1/DLP/v23042736_v125428396/Stopping-an-Enforce-Server-on-Windows?locale=EN_US
NEW QUESTION 16
Which two Network Discover/Cloud Storage targets apply Information Centric Encryption as policy response rules?
Answer: AD
NEW QUESTION 17
How should a DLP administrator change a policy so that it retains the original file when an endpoint incident has detected a “copy to USB device” operation?
Answer: A
NEW QUESTION 18
A DLP administrator created a new agent configuration for an Endpoint server. However, the endpoint agents fail to receive the new configuration. What is one possible reason that the agent fails to receive the new configuration?
Answer: C
NEW QUESTION 19
What is required on the Enforce server to communicate with the Symantec DLP database?
Answer: D
Explanation:
Reference: https://www.symantec.com/connect/articles/three-tier-installation-dlp-product
NEW QUESTION 20
Which two actions are available for a “Network Prevent: Remove HTTP/HTTPS content” response rule when the content is unable to be removed? (Choose two.)
Answer: AE
NEW QUESTION 21
A divisional executive requests a report of all incidents generated by a particular region, summarized by department. What does the DLP administrator need to configure to generate this report?
Answer: A
NEW QUESTION 22
What detection technology supports partial row matching?
Answer: D
Explanation:
Reference: https://www.slideshare.net/iftikhariqbal/technology-overview-symantec-data-loss-prevention-dlp
NEW QUESTION 23
What is the correct configuration for “BoxMonitor.Channels” that will allow the server to start as a Network Monitor server?
Answer: C
Explanation:
Reference: https://support.symantec.com/en_US/article.TECH218980.html
NEW QUESTION 24
Which two locations can Symantec DLP scan and perform Information Centric Encryption (ICE) actions on? (Choose two.)
Answer: CD
Explanation:
Reference: https://www.symantec.com/content/dam/symantec/docs/data-sheets/information-centric-encryption-en.pdf
NEW QUESTION 25
Under the “System Overview” in the Enforce management console, the status of a Network Monitor detection server is shown as “Running Selected.” The Network Monitor server’s event logs indicate that the packet capture and filereader processes are crashing.
What is a possible cause for the Network Monitor server being in this state?
Answer: D
NEW QUESTION 26
......
P.S. Certleader now are offering 100% pass ensure 250-438 dumps! All 250-438 exam questions have been updated with correct answers: https://www.certleader.com/250-438-dumps.html (70 New Questions)